How to Secure Your Files: A Comprehensive Guide
Title: How to Secure Your Files: A Comprehensive Guide
In an increasingly digital world, documents and files comprise a significant part of your business operation. Whether these files hold sensitive client information, confidential financial data, or proprietary business techniques and strategies, it is crucial that they remain secure. A breach could result in significant financial loss, a damaged reputation, or, in some cases, legal action. With recent high-profile data breaches drawing attention to this problem, it's clear that every organization should be taking steps to secure their files. Here is a comprehensive guide to safeguarding your data and ensuring your files are secure.
###Understanding the Risks
The first step toward securing your files is understanding the risks you're facing. Malware is a common threat, often encrypting your files and demanding a ransom in return for the decryption key. Phishing scams trick employees into revealing sensitive data, including login details for the company’s secure file system. Insider threats also pose a risk, with disgruntled or careless employees potentially leaking data, either accidentally or intentionally.
###Implementing Access Controls
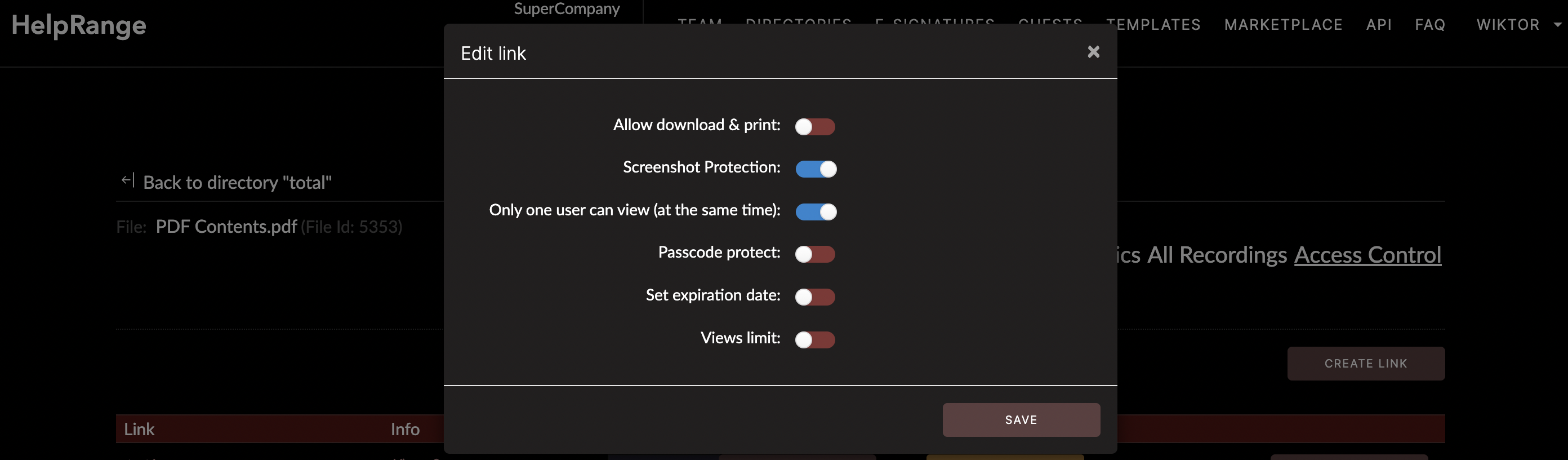
A critical aspect of file security is ensuring that only the right people have access to specific files. Setting access controls helps prevent unauthorized users from accessing sensitive data. Access controls can be as simple as setting up a password for a document or as complex as configuring multi-factor authentication systems.
###Encrypting Your Files
Encrypting your files is an excellent measure to ensure that even if your files do get accessed by unauthorized persons, they won't be able to use the information. Encryption works by translating data into a code that only can be read by individuals who possess the encryption key. Many software solutions offer the ability to encrypt documents, including tools like Microsoft Office or Adobe.
###Ensuring Regular Backups
Sometimes, the best defense is a good offense. Regularly backing up your data makes sure that even if your data is compromised or destroyed, you can recover quickly and effectively with minimum impact on your business operations.
###Utilizing Secure File Transfer Procedures
When transferring files, especially over the internet, there's a risk of them falling into the wrong hands. Therefore, it's crucial to use secure file transfer procedures for sending or receiving files. Such procedures can include email encryption or using FTPS (File Transfer Protocol over SSL).
###Taking Advantage of PDF/ Document Protection Tools
A variety of PDF/document protection tools offer features that help secure your files. These tools don't just protect your files from unauthorized access; the more advanced among them also provide usage analytics, enabling you to track who has accessed your documents and what they did with them.
One powerful tool offering such features is HelpRange, an online service that allows you to control and track your documents in real-time. HelpRange is an effective solution if you're handling PDFs; it not only secures your documents but also provides insight into how your files are being used, thus providing comprehensive security and usage analytics.
###Educating Employees
Last, but certainly not least, it's vital to educate your employees about the importance of file security. After all, even the most sophisticated security systems won't protect your files if your employees don't know how to use them correctly. Regular training on phishing awareness, password security, safe internet usage, and secure file transfer procedures can go a long way towards reducing the risk of a data breach.
In conclusion, file security is an essential aspect of running a modern business. By implementing access controls, encrypting files, ensuring regular backups, using secure file transfer procedures, utilizing PDF/document prediction tools, and educating your personnel, you can significantly reduce your risk of a catastrophic data breach. While it's impossible to be 100% secure, following these guidelines can give you a robust defense against most common threats.
Check out HelpRange
HelpRange is "Next-Gen Documents Protection & Analytics Platform". HelpRange represents the cutting-edge platform for document access controls and in-depth analytics, ensuring superior management and usage insights for your documents.
