Secure, External Document Sharing
Secure, external document sharing is the process of sharing sensitive or confidential documents
with others in a secure and encrypted manner. This ensures that only authorized
individuals have access to the information contained within the documents and that the
information is protected from unauthorized access or modification.
One popular method of secure, external document sharing is through the use of virtual private
networks (VPNs). A VPN is a secure and encrypted connection between two devices, such as
a computer and a server, that allows for the safe and secure sharing of documents. By
using a VPN, the documents being shared are encrypted and can only be accessed by those
with the proper decryption key.
Another method of secure document sharing is through the use of cloud-based services
such as Dropbox, Google Drive, and OneDrive. These services allow users to store and
share documents in the cloud, and typically offer encryption options to protect the
documents from unauthorized access.
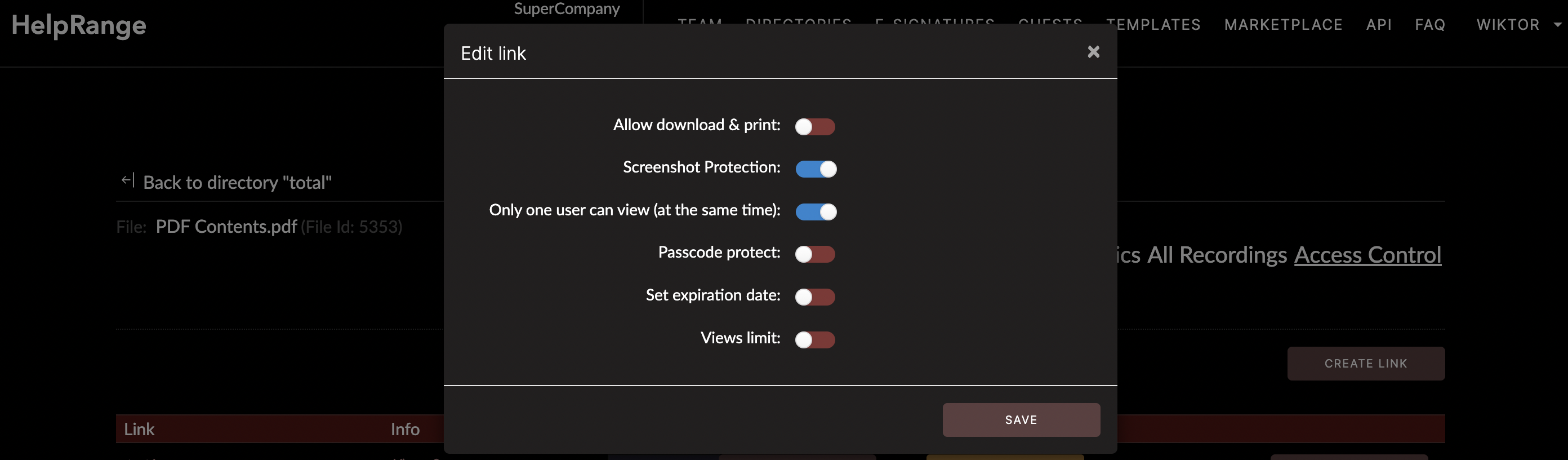
In addition to these methods, there are also specialized software and apps that can be
used for secure document sharing. These include apps like Signal and WhatsApp, which
use end-to-end encryption to protect the messages and documents being shared. There are
also apps like HelpRange (our tool) or DocSend, more focused on businesses, which allows
for adding passwords and setting secure shareable links.
When choosing a method of secure document sharing, it's important to consider the
level of security and encryption offered, as well as the ease of use and compatibility
with the devices and platforms being used. Additionally, it's important to ensure that
the service or software being used is reputable and has a good track record of
protecting user data.
A Few Words Of Summary
In conclusion, secure document sharing is an important tool for protecting sensitive
or confidential information from unauthorized access or modification in external environment. By using VPNs,
cloud-based services, or specialized software, individuals and organizations can ensure
that the documents they share are protected and only accessible to authorized
individuals.
